This article applies to:
- SEG Cloud
Question:
- How can I set up a blacklist or whitelist?
- How can I block mail from some addresses or servers?
- How can I make sure that mail from some addresses or servers is not blocked as spam?
Reply:
Whitelists:
To bypass spam checking for certain external addresses or server IP addresses:
- In the SEG Console, navigate to Policy Elements > Groups.
- Create a new External user group, and add email addresses you want to whitelist.
- Optionally create a new IP group, and add IP addresses or ranges you want to whitelist.
- Go to Customer Packages / Standard Protection.
- Click User Matching next to the "Anti-Spam (Inbound)" Policy.
- Click "Apply to users matching...", and then check "Except where addressed from groups".
- Click groups.
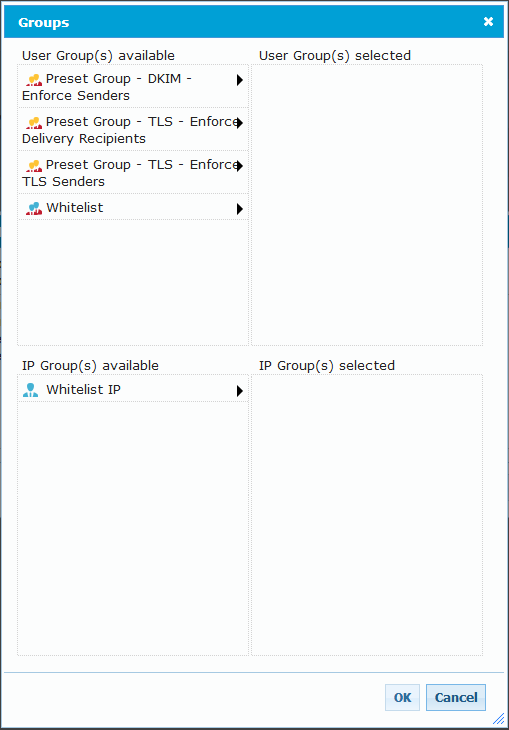
- On the group window, click the arrow next to each of the groups you created above, and move them to the "selected" list.
- Click OK, then OK again.
Note: This whitelist will only bypass spam checking. If you wish to bypass specific rules, add User Matching to those rules directly.
Blacklists:
To quarantine all messages from certain email addresses or server IP addresses:
- In the SEG Console, navigate to Policy Elements > Groups.
- Create a new External user group, and add email addresses you want to blacklist.
- Optionally create a new IP group, and add IP addresses or ranges you want to blacklist.
- Go to Customer Packages / Standard Protection / Customer Blacklist (Inbound)
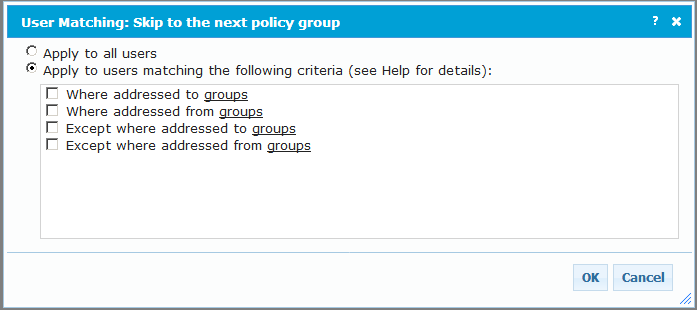
- Click User Matching next to the first rule in this policy (The rule is named Skip to the next policy group).
- Click "Apply to users matching...", and then check "Except where addressed from groups".
- Click groups.
- On the group window, click the arrow next to each of the groups you created above, and move them to the "selected" list.
- Click OK, then OK again.
Notes:
- Anti-Virus/Malware checking cannot be bypassed.
- Changes to rules are applied within approximately 20 minutes.
- Changes to group membership are applied within approximately five minutes.
Trustwave MailMarshal Cloud KB article Q20202
Last Modified: April 8, 2018